
On May 7, 2025, Ethereum — the world's second-largest blockchain network — activated a major upgrade called Pectra. EIP-7702 was the most significant change in that upgrade: it allows ordinary crypto wallets to do much more than before, similar to upgrading from a basic phone to a smartphone.
But within days of EIP-7702 going live, hackers were already exploiting it. In just the first three months: over $12 million drained from more than 15,000 wallets, and one person lost $1.54 million from a single mistaken click.
EIP-7702 itself is not the problem — the problem is that most users don't understand it, while hackers understand it very well. This article explains EIP-7702 in plain terms so you know what risks you're facing and how to check eip-7702 on your wallet and revoke it.
What Is EIP-7702
To understand EIP-7702, it helps to first understand how your crypto wallet currently works.
Your MetaMask, OKX, or Trust Wallet is essentially a digital lockbox. You use a private key — a secret string of characters, the equivalent of a house key — to unlock it, sign off on transactions, and move funds. Simple and secure, but limited: it can only do one thing at a time, like a box with a single compartment.
There's another type of wallet called a smart contract wallet (such as Safe or Argent). These wallets can execute multiple commands at once, automate actions, and set complex conditions — like a multi-compartment intelligent safe. The problem is that to use one, you have to create a completely new wallet address and transfer all your assets there. That's inconvenient, and many people don't want to change their existing address.
EIP-7702 solves that problem. It lets your ordinary wallet "borrow" smart contract capabilities — without changing your wallet address or moving your assets anywhere. Your existing MetaMask address stays the same, but it can suddenly do much more.
The mechanism behind this is called delegation — think of it as granting authorization. Your wallet authorizes another program (a smart contract) to act on its behalf when a transaction occurs, following rules that are programmed into that contract in advance.
How Does EIP-7702 Work?
The delegation mechanism — your wallet authorizes someone to act on your behalf
Imagine signing a power of attorney document for a property manager. The document states: "This person is authorized to make transactions on my behalf under the following conditions." From that point on, whenever a transaction involving your assets occurs, the manager steps in and handles it — according to the rules written in the document — instead of you doing everything manually.
EIP-7702 works on the same logic. When you set up a delegation, you're writing an invisible label into your wallet. That label tells the Ethereum network: "From now on, whenever a transaction involves my wallet, follow the instructions of Program X — instead of just transferring funds as usual."
Program X could be something completely legitimate — like Rabby Wallet's system that bundles multiple transaction steps into one to save you money. Or it could be a malicious program built by a hacker, designed to automatically drain everything from your wallet the moment funds arrive.
The single most important thing to remember: that authorization label is created with just one signature. Once signed — whether intentionally or by mistake — your wallet has authorized that program to act on your behalf until you actively revoke it.
Real-world legitimate uses — why EIP-7702 is good when used correctly
When used for the right purpose, EIP-7702 is genuinely useful. Every major wallet and DeFi application has already integrated it.
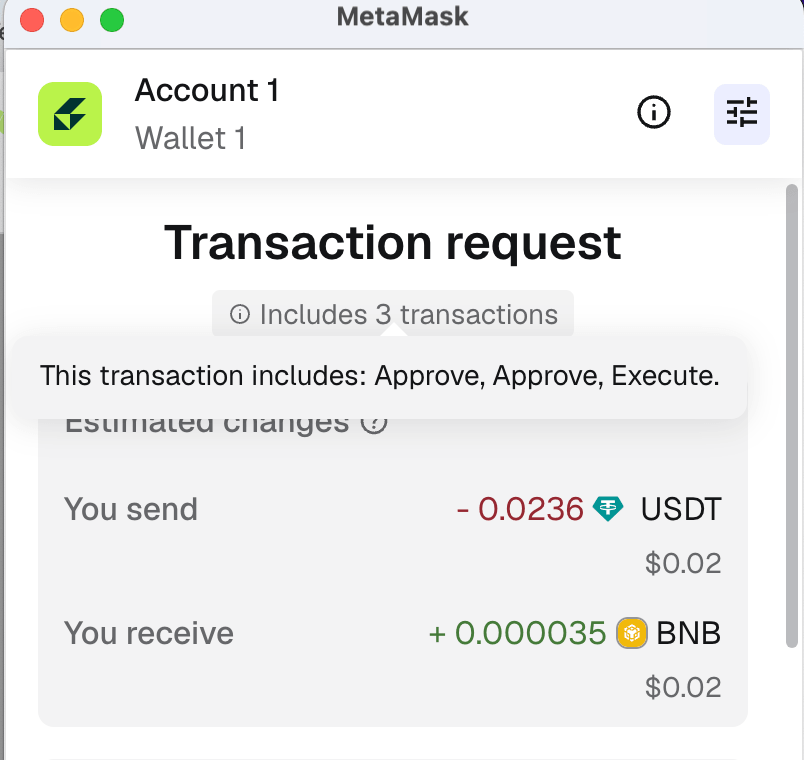
MetaMask implements EIP-7702 as an optional "smart account" feature you can turn on or off. When enabled, your wallet can batch multiple transactions together, or pay gas fees using USDC instead of requiring ETH every time.
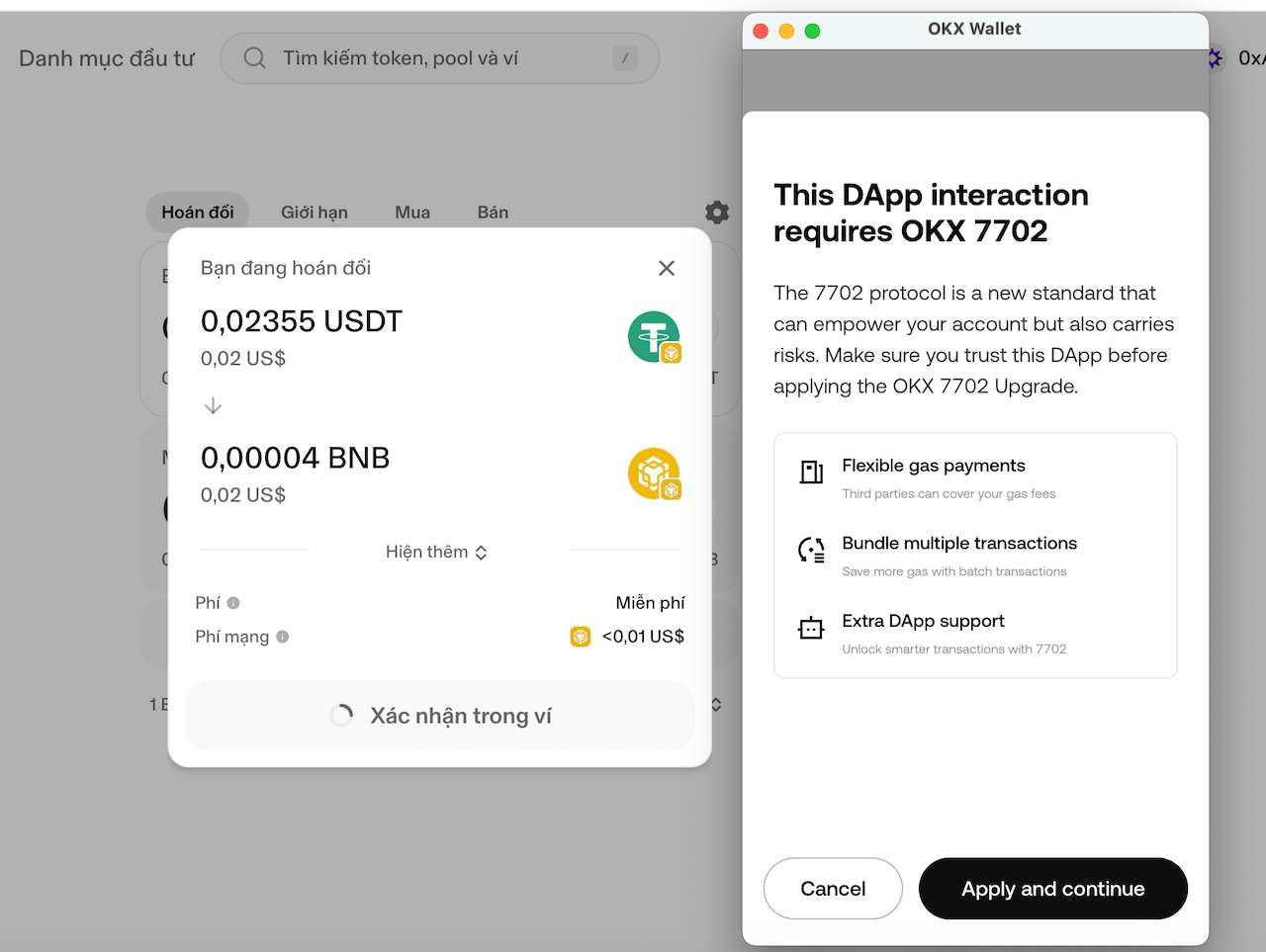
OKX Wallet built its entire next-generation wallet engine on EIP-7702, with open-source code on GitHub — one of the first wallets to complete the integration right after Pectra.
Safe (Gnosis Safe) lets you upgrade your regular wallet to a multi-signature wallet — meaning 2 or 3 people must all approve a transaction before it goes through, which is much safer for organizations or groups managing shared funds — without creating a new wallet address or moving assets.
Uniswap integrated EIP-7702 into its swap interface so users can approve and swap tokens in a single action, instead of the two separate steps required before.
Beyond batching transactions, EIP-7702 unlocks two more capabilities that regular wallets simply can't do:
Pay gas fees with any token — instead of always needing ETH to cover transaction fees, you can use USDC, USDT, or any other token. A practical example: you want to swap USDC for ETH but your wallet has no ETH for gas — with a smart account enabled, the wallet handles the fee automatically without you needing to top up ETH first.
Execute complex DeFi strategies in a single transaction — borrow USDC from Aave, use that USDC to buy ETH on Uniswap, then stake the ETH on Lido — all in one confirmation, instead of doing each step separately and waiting for each transaction to confirm on its own.
This is a genuinely positive direction for crypto users. The problem comes when the same mechanism is weaponized to take control of wallets.
How Attackers Weaponize EIP-7702
Remember the power of attorney example? The key problem is that Ethereum doesn't verify whether the "authorized manager" in that document is trustworthy or malicious — it simply executes whatever is written. Hackers exploit exactly this.
Here's the playbook they use — deceptively simple, but extremely effective:
Step 1 — Build a fake website that looks identical to a popular DApp: Uniswap, PancakeSwap, or Blur. The interface is indistinguishable from the real thing — correct logo, correct colors, correct layout. The only difference is the URL, which most users don't check closely.
Step 2 — The site asks you to confirm a transaction with a completely reasonable-sounding reason: "swap tokens," "activate a new wallet feature," or "upgrade to smart account to receive your airdrop." A confirmation popup appears from MetaMask — it looks exactly like every other popup you've seen.
Step 3 — Hidden inside that transaction is an EIP-7702 delegation command that grants control of your wallet to the hacker's malicious program. When you click "Confirm" — you've just handed over full control of your wallet without knowing it.
Step 4 — From that moment on, every ETH sent to your wallet automatically flows to the hacker's address. Tokens can be drained at any point, without any further action required from you.
This is far more dangerous than a standard token approval scam. A normal token approval only lets attackers take one specific token. EIP-7702 delegation grants full control of your entire wallet — every token, all ETH, every NFT — with a single signature.
There's one more thing that makes it worse: hackers can configure the delegation in a special way that makes it work across multiple blockchains simultaneously — Ethereum, BSC, Arbitrum, Base — instead of just one. Sign once on one network, and lose funds across all of them.

Real EIP-7702 Hacks That Already Happened
This isn't theoretical. In the first three months after Pectra, real losses reached tens of millions of dollars.
The $1.54M Loss — One Signature, Everything Gone (May 2025)
The victim accessed a website that mimicked Uniswap and performed what looked like a routine token swap. The interface was normal, the confirmation popup was normal — nothing seemed unusual until they clicked "Confirm."
What was actually hidden inside that "swap" transaction was an EIP-7702 delegation command that handed control of the wallet to the attacker. The moment the user confirmed, the malicious program automatically executed a chain of actions — approving all tokens for transfer, moving NFTs, and installing an automatic ETH redirect to the hacker's wallet. The entire process took about 12 seconds. Total loss: $1.54 million.
Full breakdown: Security analysts warn about EIP-7702 flaw after user loses $1.54M — Cryptopolitan
Inferno Drainer — Professional Hackers Target MetaMask Users
Inferno Drainer is one of the largest "hacking-as-a-service" operations in the crypto underworld — they build attack tools and rent them out to other hackers in exchange for a cut of stolen funds. The moment EIP-7702 launched, the group immediately developed a toolkit specifically for this new standard.
Their technique was particularly clever: instead of using a completely unknown contract address that users might notice, they exploited the legitimate MetaMask delegation address — something users already recognized and trusted. Victims saw a transaction referencing the familiar MetaMask address, felt no concern, and confirmed. In reality, they had just authorized the group to drain all their tokens without any further prompts.
A second malicious contract from the same group installed an automatic ETH redirect: any ETH sent to the victim's wallet — even gas deposited to pay for another transaction — was swept away to the hacker in the same instant, before the victim's own transaction could execute.
Full technical analysis: Inferno Drainer Exploits Ethereum EIP-7702 in Evolving Phishing Tactics and Inside Wallet Drainers and EIP-7702 Exploits — ThreeSigma
August 2025 — $12M in 31 Days
This was the worst month since Pectra launched. According to Cryptopolitan and AMBCrypto:
- $12 million drained in August 2025 — a 72% increase from July
- 15,230 wallets attacked, with the single largest individual loss reaching $3 million
- 80–97% of EIP-7702 delegation contracts on Ethereum mainnet identified as malicious — meaning the vast majority of currently delegated wallets are under attack
- 450,000+ wallet addresses compromised since May 7, 2025
The 450,000 figure is particularly alarming because most victims had no idea their wallet had been delegated until the money was gone.

The Most Dangerous Scenario: Exposed Private Key + EIP-7702 Bot Already Waiting
This is the scenario Airdrop101 encounters most often — and the hardest to recover from, because the victim hasn't done anything wrong recently.
The reality is that millions of crypto wallets are quietly being monitored by hackers. These wallets had their private key or seed phrase exposed at some point in the past — through a fake wallet app downloaded once, a seed phrase entered on an unfamiliar website, or a cloned wallet used briefly and forgotten. Hackers maintain lists of these addresses. But instead of draining them when the balance is low, they wait.
They quietly install an EIP-7702 delegation into the wallet — and since they already have the private key, they don't need the victim to sign or confirm anything. The wallet still looks completely normal from the outside. The balance still shows up. Transactions still appear to work. But a trap is already set inside.
Then, when a large airdrop arrives, when staking rewards return to the wallet, or when the victim sends funds there — the trap activates:
- Deposit ETH to pay for a transfer out? → The hacker's bot sweeps that ETH in the same instant, before your transaction can even be processed. You cannot do anything.
- Airdrop tokens land in the wallet? → The bot claims them first, or drains them within seconds of arrival.
- Receive any new tokens? → Automatically redirected to the hacker's wallet, with no prompt or warning.
This is exactly what happened to many WLFI token holders. When the airdrop was distributed to their original wallets — the ones already compromised — users found themselves completely stuck. The presale wallets were locked and couldn't be changed, and every attempt to deposit gas and rescue the tokens failed: the gas was swept away first. Security researcher Yu Xian described the situation precisely: "even when the victim tries to transfer the remaining tokens, the gas you deposit will be automatically transferred away before your transaction executes."
What makes this scenario uniquely dangerous is that you don't have to do anything wrong right now to be affected. A single security mistake from months or even years ago — a seed phrase entered on an unfamiliar site, a trial wallet used once and forgotten — is all it takes for a hacker to install a trap and wait for a major airdrop.
If you have old wallets that have been used across multiple platforms, wallets where you once entered your seed phrase online, or wallets you're expecting airdrop distributions to — check them immediately with the EIP-7702 Checker. More detail on this attack pattern: analysis on Binance Square.
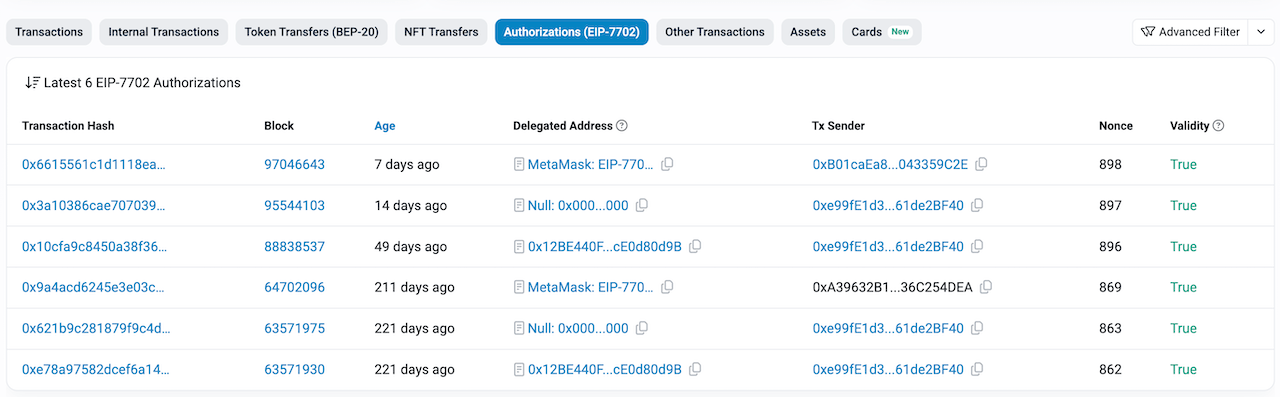
How Do I Know If My Wallet Has Been EIP-7702 Delegated?
The good news is you can check right now, for free, without connecting your wallet to anything — you only need to enter your public wallet address.
Before checking, here are some warning signs worth noting:
- ETH transferred into your wallet disappears immediately with no transaction you initiated
- Unfamiliar transactions appearing in your wallet history that you don't remember making
- Tokens showing as "approved" for an address you don't recognize
Whether you notice these signs or not, the most reliable way to be sure is to use the free EIP-7702 delegation checker from Airdrop101. It scans 17 blockchain networks simultaneously — Ethereum, BSC, Arbitrum, Base, Polygon, Optimism, and 11 more — and tells you whether your wallet is currently delegated to any program, and whether that program belongs to a legitimate application.
Enter your wallet address, hit check, get results in 15 seconds.
5 Warning Signs You're About to Fall for an EIP-7702 Scam
Hackers follow the same playbook every time. Recognize these 5 patterns and you avoid the vast majority of risk:
-
A website asking you to "upgrade your wallet to a smart account" — no legitimate DeFi application needs you to upgrade your wallet through an external website. Smart account features are only enabled through your own wallet app's official interface (Rabby, Safe, MetaMask). If you see this request from any other website, it's a trap.
-
An email or message about a "mandatory post-Pectra wallet migration" — Ethereum upgrades happen automatically at the network level. Users don't need to do anything. Any message claiming you must act immediately to avoid losing funds is a scam.
-
A confirmation popup showing an unfamiliar "authorization list" — a normal token swap transaction doesn't include this. If your wallet shows an extra list of unknown addresses in the confirmation window when you're only trying to swap tokens, reject it and leave the site immediately.
-
A URL that doesn't match the real DApp's address — Uniswap is
uniswap.org, notuniswap-v4.ioorapp-uniswap.net. Before confirming any transaction, look at the browser address bar and verify the URL carefully. -
A popup offering "EIP-7702 airdrop claims" — no legitimate airdrop requires you to set up a delegation. This is the most common social engineering angle used in 2025, exploiting the fear of missing out on airdrops to get users to sign without reading carefully.
My Wallet Is Already Delegated — What Should I Do Right Now?
Stay calm. A delegation does not mean your assets are already gone. If you catch it early, there's still time to act.
Revoke immediately using Rabby Wallet
The fastest and safest method is to use Rabby Wallet to send a special revocation command — essentially, this overwrites the old "authorization label" with a blank one, which means wiping out all delegations that were previously set. After that, your wallet returns to normal, exactly as it was before EIP-7702 existed.
Step-by-step guide: how to revoke EIP-7702 delegation with Rabby Wallet.
Very important note: Before revoking, transfer all assets out of the compromised wallet first. Here's why: if the hacker installed an automatic ETH redirect, even the small amount of ETH you deposit to pay for the revocation transaction could be swept away before your command executes. If you're in that situation, a technique called bundle transaction is needed to resolve it — contact Airdrop101 for help.
Wallet already drained — is there still hope?
Even when assets have been partially drained, it doesn't necessarily mean everything is lost. Specifically for unclaimed airdrops, tokens in a vesting schedule (locked and releasing gradually over time), or assets currently staked — timely intervention can still recover them.
Airdrop101 has helped users successfully recover assets even from actively compromised wallets — including ERA (ZKSync) and RECALL — in situations where the users themselves had already given up.
If you're in this situation, reach out directly for a free on-chain assessment: t.me/trangchongcheng.
Can an EIP-7702 Delegation Be Fully Revoked?
Yes — and this is actually good news compared to many other types of crypto attacks.
EIP-7702 delegations are not permanent. The authorization can be completely cleared at any time, as long as you still control the wallet (still have the private key). After revoking, the wallet operates exactly as it did before EIP-7702 existed — nothing left over, no trace.
You can either:
- Remove the delegation entirely — wallet goes back to being a standard wallet with no authorizations
- Replace it with a legitimate one — for example, delegating to Rabby to use valid batch transaction features
One practical thing to know: MetaMask and OKX Wallet don't currently support revoking EIP-7702 delegations through their standard interface. You need Rabby Wallet to do this. Alternatively, you can revoke directly through the EIP-7702 Checker — connect Rabby Wallet and click revoke right inside the tool.
Conclusion
EIP-7702 is a genuine step forward for Ethereum. It gives ordinary wallets smart contract capabilities, reduces the number of times you need to sign transactions, and lays the groundwork for a much more user-friendly generation of DeFi applications.
But as with every new technology, attackers always arrive before ordinary users. Three things to remember:
- Delegation doesn't happen by itself — you have to confirm a transaction for it to occur. Be careful with any transaction from an unfamiliar website, especially if you notice an extra authorization list in the confirmation window.
- Catching it early means it can be fixed — delegation can be fully revoked as long as you still control the wallet and act before everything is drained.
- Old wallets need checking now — especially ones used across multiple platforms, or any wallet you're expecting an airdrop to land in.
Check your wallet now at the EIP-7702 Checker — free, no wallet connection needed, scans 17 blockchains simultaneously. If you find a suspicious delegation or your wallet has been drained, revoke token approvals and contact us directly for support. Don't wait until it's too late.